Live guard intrusion response is a multi-stage security process where AI detection, human verification, and real-time intervention work together to stop crime as it unfolds. When a live guard spots an intruder, the sequence moves from automated alert to visual confirmation to active deterrence within seconds.
This guide covers AI-powered detection and alert delivery, live guard verification and threat assessment, two-way audio intervention, law enforcement escalation, property-specific response protocols, post-incident evidence preservation, and the advantages of proactive monitoring over passive surveillance.
AI-driven cameras continuously scan for motion, classify detected objects, and filter out environmental false alarms before sending a consolidated alert package to the guard. The guard receives the live feed, flagged zone, and object classification instantly, eliminating the need to search across camera views manually.
Within seconds of receiving an alert, the trained operator confirms the threat through live and buffered footage, logs the intruder’s physical description, behavior, and direction of movement, then initiates a direct verbal warning through on-site speakers. Specific, personalized audio commands referencing the intruder’s exact location and appearance trigger immediate flight in nearly all cases.
When escalation is required, the guard contacts 911 with verified details, including suspect descriptions, entry points, and live video access. Continuous monitoring during police response keeps dispatchers updated on suspect movement until officers arrive.
Response protocols adapt based on property type; commercial sites prioritize multi-zone perimeter coverage, residential properties focus on occupant safety, and high-value facilities enforce zero-tolerance escalation timelines. After resolution, timestamped footage and detailed incident reports are preserved through documented chain-of-custody procedures for legal admissibility. Proactive monitoring then uses incident data to refine detection patterns and prevent repeat intrusions.
How Does AI Detection Trigger the Initial Intruder Alert?
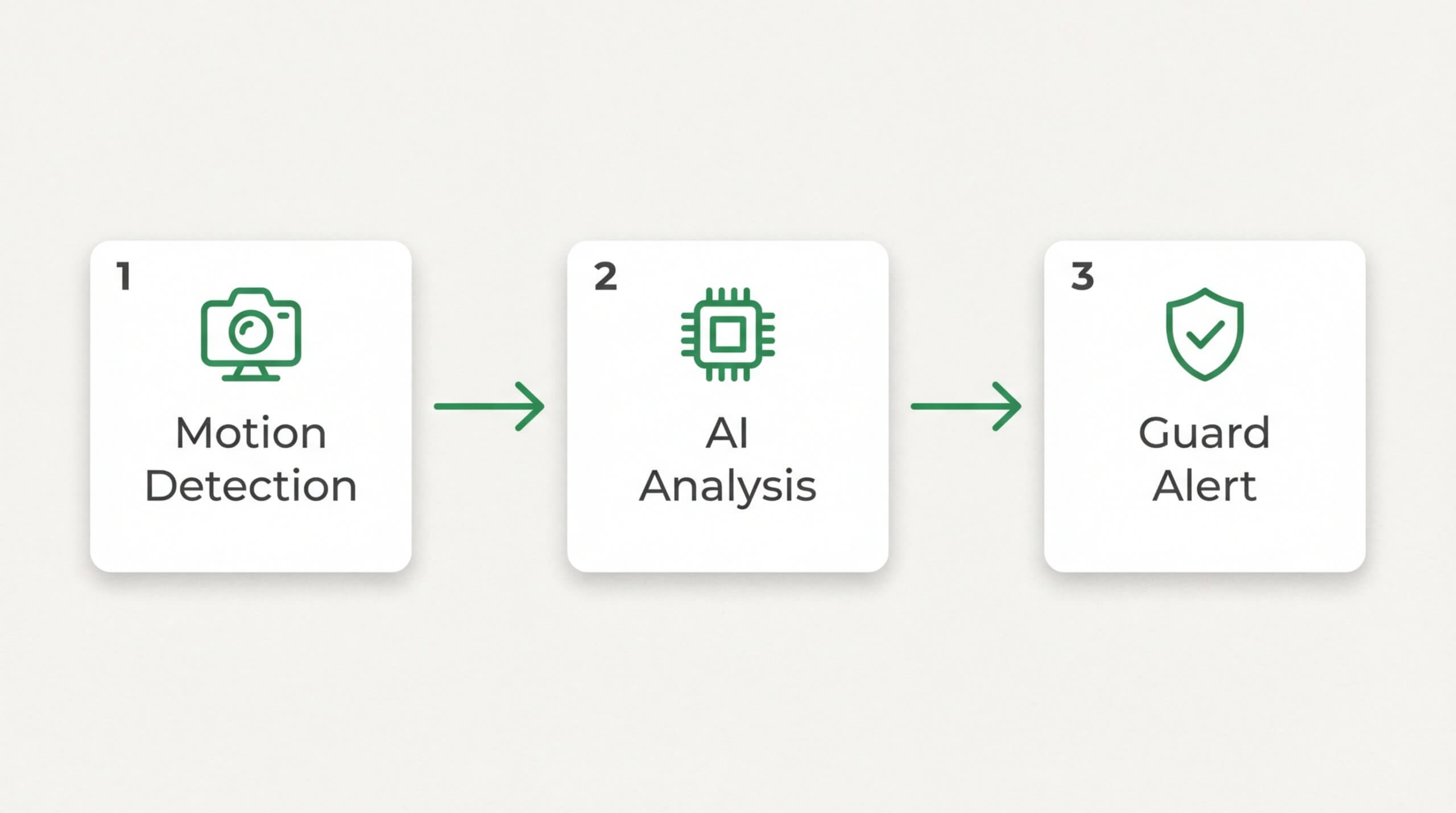
AI detection triggers the initial intruder alert by using motion-sensing cameras and video analytics to identify suspicious activity, filter out false alarms, and relay verified threat data to a live guard. The process involves three stages: motion flagging, threat classification, and alert delivery.
What Role Does Motion Detection Play in Flagging Activity?
Motion detection plays the foundational role in flagging activity by serving as the first sensor layer in a remote guarding system. AI-powered cameras continuously scan defined zones for pixel changes that indicate movement. When motion crosses a preset threshold, the system instantly generates an event flag.
These flags do not go directly to a human operator. Instead, the AI analytics engine receives each motion event and begins classifying it. Without this initial motion detection layer, every frame of footage would require manual review, making real-time response impossible. Motion detection narrows the data stream so that only meaningful events move forward for analysis.
How Does AI Distinguish Between a Real Threat and a False Alarm?
AI distinguishes between a real threat and a false alarm by analyzing the shape, size, behavior, and trajectory of detected objects against trained classification models. The system categorizes motion sources into people, vehicles, animals, or environmental movement.
Environmental triggers like swaying trees, shifting shadows, or rain are filtered out automatically. According to Lumana AI, AI video analytics platforms can achieve false alarm reduction rates of 85–90% or higher by distinguishing genuine threats from harmless motion. This precision ensures that only credible intrusion events reach the live guard’s screen, preventing alert fatigue and keeping response times fast. For most properties, this filtering capability is what separates a functional security system from one that simply generates noise.
What Information Does the System Send to the Live Guard?
The system sends the live guard a consolidated alert package that includes the live camera feed, the flagged object’s classification, the specific zone where the event occurred, and a timestamp. Remote guarding combines CCTV cameras, video analytics, alarms, and monitoring centers with live security agents to create a unified response workflow.
This structured data transfer means the guard does not start from scratch. They see exactly where the flagged individual or vehicle is located, what triggered the alert, and which cameras have the best angle. With verified intelligence already in hand, the guard can begin visual confirmation within seconds rather than spending time searching across multiple feeds.
What Does the Live Guard Do in the First Seconds After an Alert?
The live guard performs immediate visual verification, threat assessment, and situational analysis. The following subsections cover how guards verify intrusions on camera, what intruder details they assess, and how quickly trained operators complete the entire process.
How Does the Guard Verify the Intrusion on Camera?
The guard verifies the intrusion on camera by pulling up the triggered feed, reviewing live and buffered footage, and confirming whether the alert represents a genuine threat. Once the AI system flags motion, the operator switches to the corresponding camera view within seconds. The guard checks the buffered pre-event footage to see how the person entered the frame and whether the movement pattern suggests intentional trespassing.
Multiple camera angles help distinguish between a delivery driver approaching a door and someone testing locks or peering through windows. The guard cross-references the alert zone, time of day, and any scheduled activity logs for the property. If the footage shows a confirmed unauthorized presence, the guard escalates immediately. This layered review process prevents wasted police dispatches on harmless activity while ensuring real threats receive rapid action.
What Details Does the Guard Assess About the Intruder?
The details the guard assesses about the intruder include physical description, behavior patterns, potential weapons, number of individuals, and direction of movement. Clothing color, build, and distinguishing features are logged first because law enforcement needs this information for dispatch.
Behavioral indicators carry significant weight in the assessment:
- Attempting to conceal identity with hoods or masks signals criminal intent.
- Testing doors, windows, or gates suggests a break-in attempt.
- Carrying tools such as pry bars or bolt cutters indicates preparation for forced entry.
- Crouching, running, or moving erratically points to awareness of surveillance.
The guard also notes the intruder’s entry point and travel path across the property. For properties with multiple buildings or large perimeters, tracking direction of movement helps police intercept rather than simply respond. In practice, the most valuable detail is often what the intruder is doing, not just what they look like.
How Quickly Does a Trained Guard Complete Visual Verification?
A trained guard completes visual verification in seconds, not minutes. Remote guarding services use visual verification to shorten the time required to address security breaches, according to BOS Security. The speed advantage comes from the guard already being stationed at a monitor when the AI alert arrives, eliminating travel time entirely.
Most trained operators confirm or dismiss an alert within 10 to 15 seconds of receiving it. This speed depends on camera quality, lighting conditions, and how many angles cover the triggered zone. 4K cameras with infrared capability reduce verification time because the guard spends less effort interpreting unclear footage.
This rapid verification window is what separates live monitoring from passive recording, where footage sits unreviewed until after a crime is complete. With verification measured in seconds, the entire response chain accelerates from deterrence through law enforcement dispatch.
How Does Two-Way Audio Intervention Work During an Intrusion?
Two-way audio intervention works by allowing a live guard to speak directly to an intruder through on-site speakers the moment suspicious activity is confirmed on camera. The following sections cover what the guard says, how intruders react, and why live audio outperforms recorded alarms.

What Does the Guard Say to an Intruder Through the Speaker?
The guard delivers a firm, direct verbal warning through the speaker that identifies the intruder’s specific actions and location on the property. A typical command might be: “You in the black jacket near the west loading dock, you are on camera. Leave the property immediately. Police have been contacted.”
This level of specificity is critical. Generic warnings are easy to ignore, but when an intruder hears their exact position and clothing described, it confirms a live human is watching. According to a 2024 report from Security Today, collaborative efforts between private security businesses and public law enforcement through remote guarding profoundly impact crime prevention and response efficiency. That coordination starts with the guard’s initial verbal command.
How Do Intruders Typically React to a Live Voice Warning?
Intruders typically react to a live voice warning by fleeing the property within seconds. The sudden realization that a real person is observing their actions in real time triggers an immediate fight-or-flight response, and nearly all choose flight.
Unlike a siren or flashing light, which criminals can assess and dismiss as automated, a live human voice creates unpredictability. The intruder cannot determine how many people are watching, whether police are already en route, or what other security measures are active. This psychological uncertainty is far more disorienting than any passive deterrent. For most trespassers, the calculation shifts instantly from “Can I get away with this?” to “I need to leave now.”
Why Is Real-Time Audio More Effective Than a Recorded Alarm?
Real-time audio is more effective than a recorded alarm because it delivers a personalized, situation-specific response that criminals cannot predict or ignore. Recorded alarms follow fixed patterns; experienced intruders learn to recognize and dismiss them.
Live audio creates what American Virtual Monitoring describes as a “double strike,” where an intruder is first spotted visually and then warned audibly in real time. This layered approach reduces overnight criminal incidents because the intruder faces proof of active human surveillance, not just an automated trigger. Security cameras that integrate active monitoring are documented to be more effective at deterring crime than passive systems that only record footage. The combination of verified visual detection and direct verbal confrontation closes the gap between detection and deterrence almost instantly.
Understanding how audio intervention stops intrusions in progress sets the stage for what happens when the guard must escalate to law enforcement.
What Happens When the Guard Escalates to Law Enforcement?
The guard escalates to law enforcement by contacting 911 dispatchers with verified threat details, live video access, and continuous real-time updates. The following subsections cover what information is relayed, how video accelerates police response, and whether monitoring continues during dispatch.
What Information Does the Guard Relay to 911 Dispatchers?
The guard relays to 911 dispatchers a verified, real-time account of the intrusion, including specific details that passive alarm systems cannot provide. Key information typically includes:
- Exact property address and the specific entry point or area of activity.
- Number of intruders observed on camera.
- Physical descriptions such as clothing, build, and direction of movement.
- Whether the intruder appears armed or is carrying tools.
- Current behavior, such as attempting forced entry, breaching a perimeter, or fleeing.
This level of detail transforms a generic alarm signal into a confirmed crime-in-progress report. Dispatchers can then assign the call higher priority, which directly influences how quickly officers are deployed.
How Does Live Video Help Police Respond Faster?
Live video helps police respond faster by providing visual confirmation that a crime is actively occurring, rather than relying on an unverified alarm signal. Dispatchers and responding officers can view the feed to assess the threat level before arrival, plan their approach, and allocate the right resources.
Unverified alarms generate enormous false-alarm volumes, which often push police departments to deprioritize alarm calls. A live video feed eliminates that uncertainty. Officers arriving on scene already know the intruder’s last known position, movement direction, and physical description. This situational awareness reduces hesitation, shortens on-site search time, and increases the likelihood of apprehension.
Does the Guard Continue Monitoring During Police Response?
Yes, the guard continues monitoring during the entire police response. The live guard tracks the intruder’s movements in real time, relaying updates to dispatchers if the suspect changes location, attempts to hide, or flees in a specific direction. This ongoing feed bridges the gap between the initial 911 call and officer arrival.
According to a 2024 Security Sales & Integration report, verified security intelligence is increasingly required by law enforcement to justify rapid response and navigate extended police response times. Continuous monitoring ensures that the information officers receive stays current, not stale. For properties with multiple camera angles, the guard can also confirm whether additional suspects have appeared or whether the site is clear.
With law enforcement coordination underway, the post-incident process preserves critical evidence for investigations.
How Does the Process Differ by Property Type?
The intrusion response process differs by property type based on asset value, layout complexity, and risk profile. Each environment requires tailored protocols.
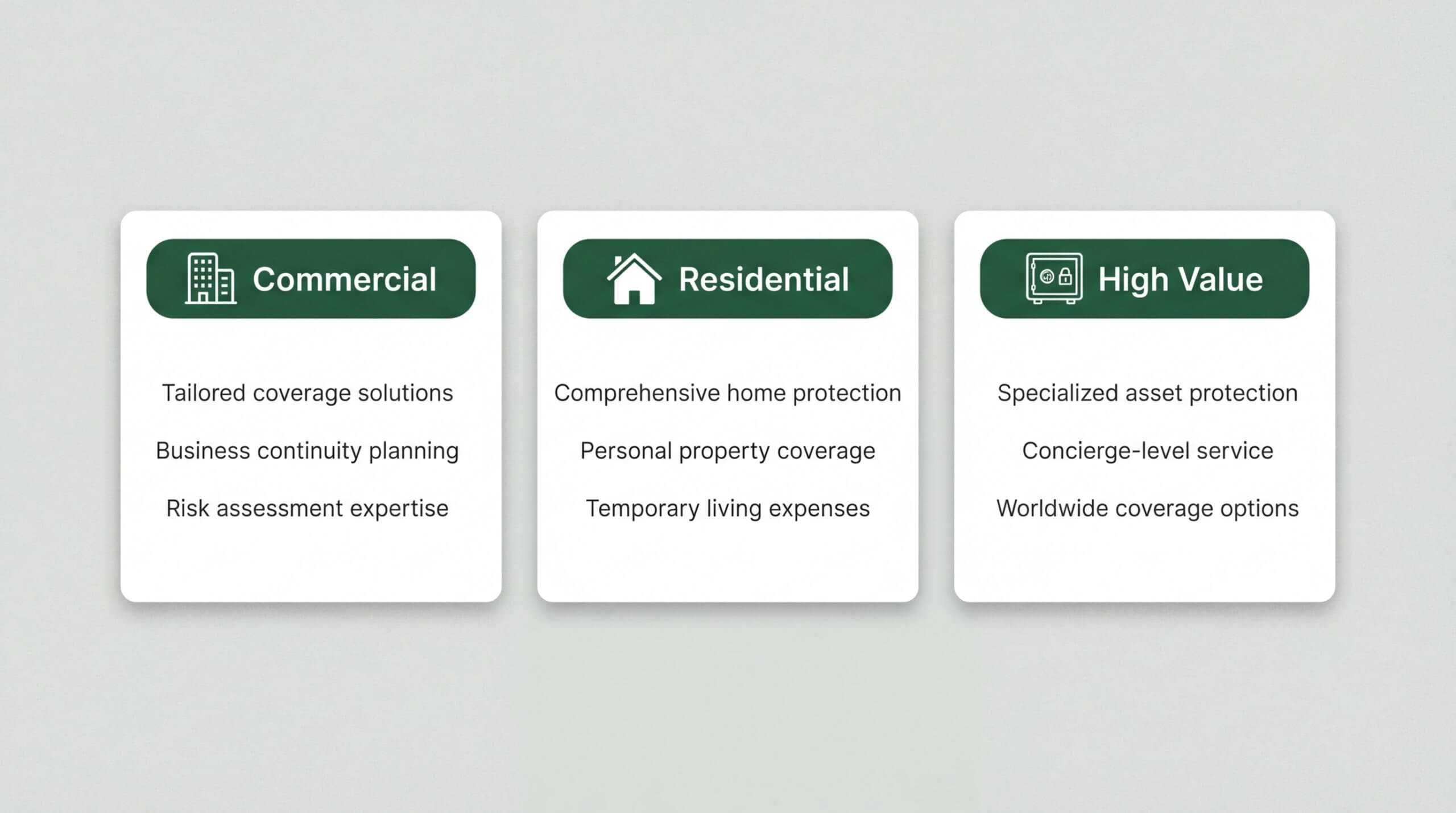
How Does Intrusion Response Work at a Commercial Property?
Intrusion response at a commercial property works by prioritizing perimeter coverage across large, multi-access facilities such as warehouses, offices, and retail locations. Guards monitor loading docks, parking areas, and entry points simultaneously using networked camera systems.
Commercial sites benefit significantly from security investment. According to research published in PubMed Central, property investments on commercial street segments can lead to larger decreases in violent crime compared to residential segments. This makes proactive monitoring especially impactful for businesses with extensive exterior exposure.
Response protocols at commercial properties typically involve:
- Activating two-way audio across multiple zones to address intruders at the exact point of breach.
- Coordinating with on-site personnel such as night managers or maintenance staff.
- Providing law enforcement with building layout details and real-time suspect tracking.
How Does Intrusion Response Work at a Residential Property?
Intrusion response at a residential property works by focusing on immediate occupant safety and rapid police notification. Guards treat every residential alert as potentially life-threatening, since homeowners or family members may be inside during a breach.
The verification process emphasizes distinguishing residents from intruders through familiar movement patterns and scheduled activity. When an unknown individual is confirmed, the guard activates audio warnings and contacts 911 with the home’s address and a live suspect description.
Residential protocols differ from commercial response in key ways:
- Privacy mode settings allow homeowners to control when monitoring is active.
- Alerts prioritize interior entry points like doors and windows over perimeter zones.
- Communication goes directly to the homeowner’s mobile device alongside law enforcement dispatch.
How Does Intrusion Response Work at a High-Value Site?
Intrusion response at a high-value site works by deploying layered security protocols calibrated to the critical nature of the protected assets. Sites such as data centers, auto dealerships, and construction yards face elevated risk due to the concentration of valuable equipment or sensitive materials.
As noted by HS Tech Group, high-value properties require specialized security approaches due to their high-risk profiles and the nature of the assets protected. Guards at these locations follow stricter escalation timelines and maintain continuous visual tracking from the moment an alert triggers.
High-value site protocols typically include:
- Zero-tolerance perimeter policies where any unauthorized presence triggers immediate audio intervention.
- Multi-camera tracking that follows a suspect across the entire facility footprint.
- Pre-established law enforcement liaison contacts for faster dispatch priority.
For every property type, the core response sequence remains the same; what changes is the urgency threshold, escalation speed, and coordination complexity tailored to each environment.
What Happens After the Intruder Leaves or Is Apprehended?
After the intruder leaves or is apprehended, the security team shifts to documentation and evidence preservation. The following subsections cover what goes into the post-incident report and how video evidence is secured for legal use.
What Does the Post-Incident Report Include?
The post-incident report includes a detailed account of the entire event, from the initial alert through resolution. This document typically covers the time of detection, guard actions taken, audio warnings issued, law enforcement communication logs, and the outcome of the intrusion attempt. It also records descriptions of the intruder, entry points targeted, and any property damage observed.
These reports serve multiple purposes: they support insurance claims, provide law enforcement with actionable intelligence, and help identify security vulnerabilities for future prevention. For property owners, a thorough post-incident report transforms a single event into a data point that strengthens long-term protection strategy.
How Is Video Evidence Preserved for Investigations?
Video evidence is preserved for investigations through a documented chain of custody that ensures footage remains legally admissible. According to Marko Law, courts require a clear chain of custody to admit video evidence, confirming that digital assets have been preserved in their original state without tampering.
Preservation involves several key steps:
- Flagging and locking the relevant footage immediately after the incident to prevent overwriting.
- Creating forensic copies stored on secure, access-controlled servers.
- Logging every person who accesses, transfers, or reviews the recordings.
- Retaining footage for the required compliance period, which often spans two years for critical incidents.
Without this rigorous process, even the clearest footage risks being excluded from prosecution. Proper evidence handling turns surveillance recordings into courtroom-ready assets that support successful legal outcomes.
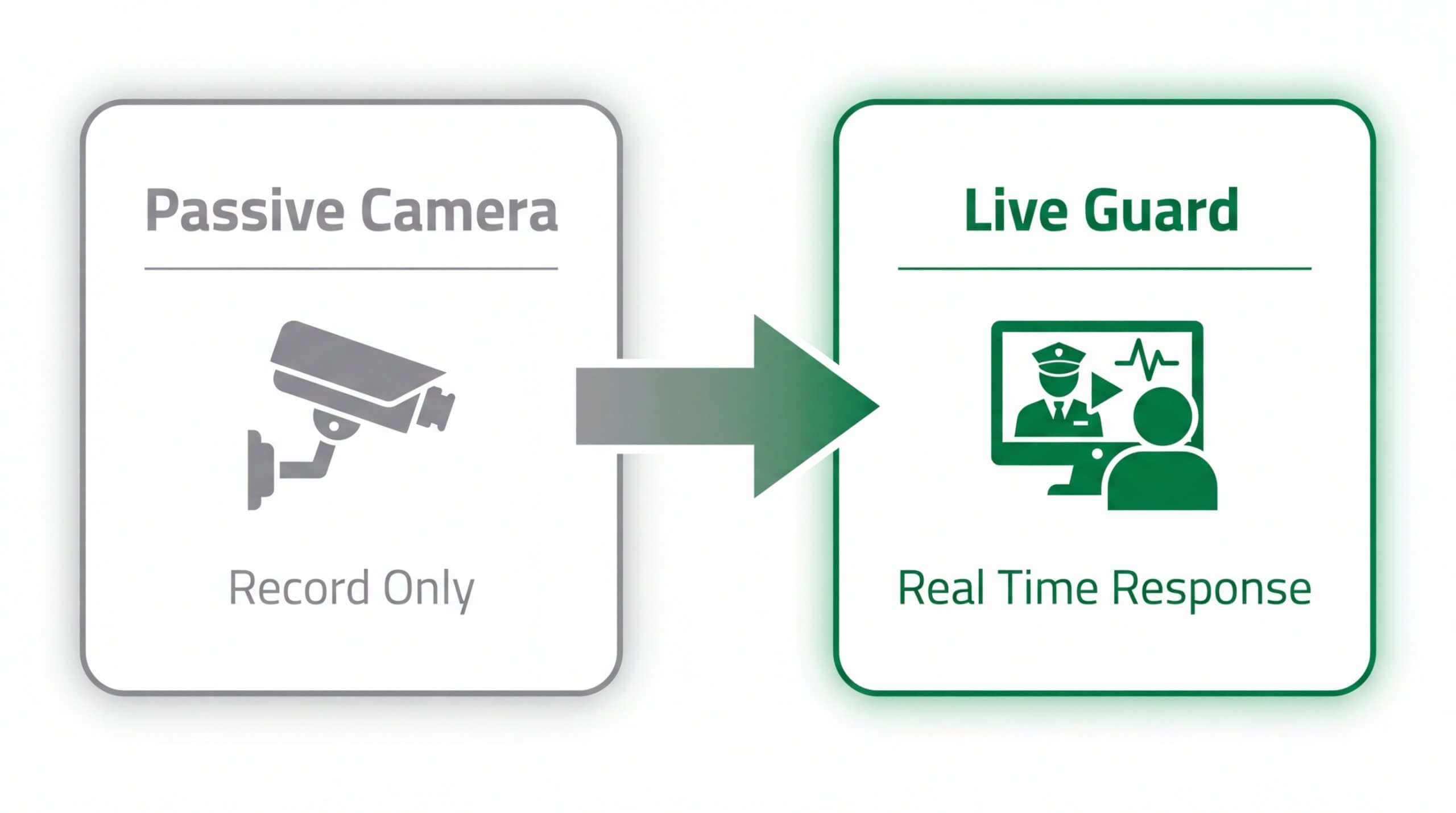
Why Do Live Guards Stop Crime When Passive Cameras Fail?
Live guards stop crime when passive cameras fail because they introduce real-time human decision-making into the surveillance loop. Passive cameras record footage but cannot intervene, warn intruders, or contact law enforcement during an active breach. A live guard transforms a camera system from a documentation tool into an active crime prevention mechanism.
The core limitation of passive surveillance is its reactive nature. Cameras that only record create evidence after a crime has already occurred, offering no deterrent to an intruder who has already committed to entering a property. Even when passive systems capture clear footage, the damage, theft, or vandalism is already done before anyone reviews the recording.
Live guards bridge this gap through verified, real-time intervention. When an alert triggers, a trained operator visually confirms the threat, issues a two-way audio warning, and escalates to law enforcement with precise details. According to Volt AI, for video evidence to maintain integrity and be legally admissible, organizations must establish and document a rigorous chain of custody from collection to the courtroom. Live monitoring ensures this chain begins at the moment of detection, not hours or days later during a footage review.
This distinction matters most during the critical window between initial intrusion and police arrival. Passive cameras offer nothing during that gap. A live guard, by contrast, maintains continuous visual tracking, provides dispatchers with real-time suspect descriptions and movement patterns, and uses audio deterrence to delay or halt the intruder’s progress. The result is a system where every second between detection and response is actively managed by a human operator rather than left to an unmonitored recording device.
Understanding this difference clarifies why proactive monitoring consistently outperforms passive alternatives in preventing property loss and enabling faster law enforcement coordination.
How Does Proactive Monitoring Prevent Repeat Intrusions?
Proactive monitoring prevents repeat intrusions by combining AI-driven detection with real-time human intervention, creating a layered deterrent that discourages return attempts. Below, we cover how this technology stops intruders before entry and the key takeaways from the live guard response process.
Can AI-Powered Live Video Monitoring Stop Intruders Before They Break In?
Yes, AI-powered live video monitoring can stop intruders before they break in. According to Pye-Barker Fire & Safety, proactive video monitoring transforms passive recording systems into active crime prevention tools by using real-time mechanisms to stop incidents before they occur. AI-powered video analytics filtering automatically identifies people or vehicles in camera feeds, reducing false positives by up to 99.95%. This precision ensures live guards receive only verified alerts, allowing immediate intervention through two-way audio warnings, strobe lights, and siren activation before a suspect reaches a door or window. For properties that have experienced prior break-ins, this capability is especially valuable; the system learns site-specific patterns and flags anomalies faster with each incident reviewed.
What Are the Key Takeaways About What Happens When a Live Guard Spots an Intruder?
The key takeaways about what happens when a live guard spots an intruder center on speed, verification, and coordinated escalation. The process begins with AI-triggered alerts, moves through rapid visual confirmation by a trained guard, and escalates to audio deterrence followed by law enforcement dispatch when necessary. According to SDM Magazine, 20 percent of intruder apprehensions occur before a suspect even gains entry into a building when audio intervention is utilized. Each step generates documented evidence, from timestamped video clips to detailed incident reports, that strengthens both legal proceedings and future prevention strategies. Pioneer Security builds this entire workflow into every monitored property, combining AI detection with live US-based guards to stop crime before it starts.